Forum Replies Created
-
AuthorPosts
-
I would start with port forwarding on your router and firewall configuration on the server. It looks like the handshake packet can’t get through.
If you had problems with v1.2.4 and don’t have them with v.1.2.5, then it was probably the same bug reported here.
Using a VPN may affect your ping, the details depend on the location of the VPN and the game server. Sometimes you can win, sometimes you can lose. Wiresock software itself has very low latency, unless you use verbose logging, don’t forget that I/O operations are always expensive.
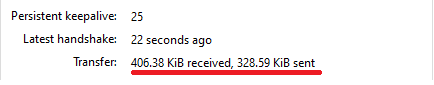
Hmm, are you sure the handshake was successful? If you’re using stock Wireguard for Windows on the client side, what tunnel statistics do you see?
I assume you have installed official WireGuard for Windows and Wiresock VPN Gateway and created the Wireguard tunnel using wg-quick-config. I also assume that port forwarding is configured on your router, and you can connect to your Wireguard server using the client application. Correct?
Please check, can you ping the Wireguard server virtual IP address from the client? It should normally work even without Wiresock VPN Gateway service running, which is only responsible for forwarding client connections to the external network.
It could also be helpful if you could share server and client configuration files (just strip endpoint and key information out).
Thanks for pointing this out. I’ve resolved the issue in v.1.2.5, please give it a try.
Thanks for testing. I’ve slightly improved the logic. Please update to v.1.1.18.
The requested extended parameter to exclude applications (DisallowedApps) was added in v.1.1.16. Please give it a try.
There are three small features that I would like to add to the next version. I hope to be ready in a week or two, depending on whether I have enough spare time.
If you have IPv6 enabled and use an IPv6 DNS (e.g. iPhone hotspot) then no traffic goes via the tunnel.
Could you please collect the wiresock application log and PCAP files for this setup and can send the files/link to [email protected]? It should help me to understand what is going on.
We can check what is going on by analyzing log and PCAP files:
Troubleshooting
If you experience any problems, then first try starting the application/service with ‘-log-level all‘ command line parameter. If you run it as an application, then it dumps the debug log directly on the console, while service will save the log into the file located in C:\ProgramData\NT Kernel Resources\WireSock VPN Client. In both cases, all processed network packets will be stored in PCAP files (can be opened and analyzed in Wireshark) in the C:\ProgramData\NT Kernel Resources\WireSock VPN Client.Please note that ‘-log-level all‘ exists for debug purposes only and significantly affects the application performance.
Typically, if the system is configured with both IPv4 and IPv6 DNS, DNS queries are sent to both. Thus, most applications should work fine. Please check if browsers are working good via wiresock and the only problem you are having is with using nslookup.
The latter seems to always default to an IPv6 DNS address if available, and this is where we have some issues.
It looks a bit unusual that a laptop has an IPv6 DNS server but no IPv4. However, this is quite a possible setup. I think I’ll just add IPv6 to IPv4 and vice versa DNS resolution to close this question.
Yes, that explains what’s going on. Wiresock does not change your network settings or add another DNS server from the WG configuration. Instead, it translates and forwards DNS requests to the DNS server from WG configuration instead of the original one. But it does not convert IPv4 DNS requests to IPv6 and vice versa. I’ll think about what can be done about it. However, if your laptop is configured with an IPv4 DNS server in addition to an IPv6 server, then all other applications (such as browsers) should work fine. NSLOOKUP should also work fine if you manually set the DNS server to any IPv4 address. For example, using
server 8.8.8.8or any other IPv4 address will force nslookup to use the DNS server from the WG configuration.Thanks for the details. One question though, how nslookup works without WG (stock or wiresock) activated? Does it try to use the IPv6 DNS servers?
-
AuthorPosts
